Understanding the Different Types of Computer Viruses
Introduction
Welcome to our comprehensive guide on understanding the different types of computer viruses. In today’s digital age, computer viruses have become a persistent threat to individuals and organizations alike. These malicious software programs can cause significant damage to your computer systems, compromise your sensitive data, and disrupt your daily operations. In this article, we will delve into the world of computer viruses, exploring their various types, characteristics, behaviors, and most importantly, how you can protect yourself from them. So, let’s start by answering the fundamental question:
What is a computer virus?
A computer virus is a type of malicious software that is designed to replicate itself and spread from one computer to another. Similar to a biological virus, it attaches itself to legitimate files or programs and infects them, causing harm to the infected system. Computer viruses can range from relatively harmless annoyances to severe threats that can result in data loss, financial damage, or even the complete shutdown of computer networks.
Common Types of Computer Viruses
Computer viruses come in various forms, each with its own unique characteristics and methods of attack. Understanding these different types is crucial in identifying and dealing with potential threats. Let’s explore some of the most prevalent types of computer viruses:
1. Boot Sector Viruses
Boot sector viruses infect the master boot record (MBR) or the bootable partition on a computer’s hard drive. These viruses execute when the computer starts up, and they can spread to other storage devices connected to the infected machine. Boot sector viruses were more common in the past but have become less prevalent due to advancements in operating system security.
2. File Infectors
File infector viruses attach themselves to executable files, such as .exe or .com files, and modify their code to include the virus’s instructions. When an infected file is executed, the virus activates and can spread to other files on the same computer or even across a network. File infectors can be particularly damaging as they can corrupt or destroy files, leading to data loss.
3. Macro Viruses
Macro viruses are often associated with applications that use macros, such as Microsoft Office programs. These viruses exploit the macro programming language to infect documents and templates. When an infected document is opened, the macro virus executes, potentially spreading to other documents and compromising the security of the system.
4. Polymorphic Viruses
Polymorphic viruses are designed to mutate and change their code to evade detection by antivirus software. Each time a polymorphic virus replicates,
changes its appearance, making it difficult for antivirus software to detect and remove it. Polymorphic viruses can also encrypt their code, making it even more challenging to detect and remove.
5. Worms
Worms are self-replicating viruses that spread across networks or the internet, often exploiting vulnerabilities in operating systems or applications. Worms can cause significant damage by consuming network bandwidth, overloading servers, or stealing sensitive data. Unlike other types of viruses, worms do not need to attach themselves to a host file to spread.
6. Trojan Horses
Trojan horses are named after the Greek myth of the Trojan horse, which was used to gain entry into the city of Troy. Similarly, Trojan horses are disguised as legitimate software or files and are designed to trick users into installing or executing them. Once installed, Trojan horses can perform a range of malicious activities, such as stealing sensitive data or providing unauthorized access to the system.
7. Spyware
Spyware is a type of virus that is designed to monitor the user’s activity on their computer and report back to the attacker. Spyware can collect sensitive data such as login credentials, financial information, and browsing habits, which can be used for malicious purposes. Spyware can be difficult to detect as it operates in the background and can often go unnoticed by the user.
8. Ransomware
Ransomware is a type of virus that encrypts the victim’s files or locks them out of their system, demanding a ransom payment in exchange for access to the data. Ransomware attacks have become increasingly common in recent years, with high-profile attacks on businesses and government organizations. Ransomware can cause significant financial damage and can be challenging to remove without paying the ransom.
Characteristics and Behavior of Computer Viruses
Understanding the characteristics and behavior of computer viruses is essential in identifying and dealing with potential threats. Let’s explore some of the key features of computer viruses:
1. Replication and Spreading Methods
Computer viruses replicate and spread in various ways, including through email attachments, infected websites, and software downloads. Some viruses can also spread through network shares, removable media, and instant messaging applications. Once a virus infects a system, it can replicate itself and spread to other computers on the same network or the internet.
2. Payloads and Damage
Computer viruses can have various payloads, depending on the attacker’s objectives. Some viruses are designed to cause system crashes or data loss, while others are intended to steal sensitive information or provide unauthorized access to the system. Some viruses can also use the infected system as part of a botnet, a network of infected computers used for malicious purposes.
3. Concealment Techniques
Computer viruses often use concealment techniques to avoid detection by antivirus software and security measures. These techniques can include encryption, polymorphism, and rootkit installation, which can make it difficult to detect and remove the virus.
4. Detection and Removal
Detecting and removing computer viruses requires the use of antivirus software and other security measures. Antivirus software can scan files and emails for known virus signatures, but may not detect new or unknown viruses. Removing a virus can be challenging, particularly if it has embedded itself deep in the system or has disabled security measures.
Prevention and Protection against Computer Viruses
Preventing and protecting against computer viruses is crucial in maintaining the security and integrity of your systems. Let’s explore some of the key measures you can take to protect yourself against computer viruses:
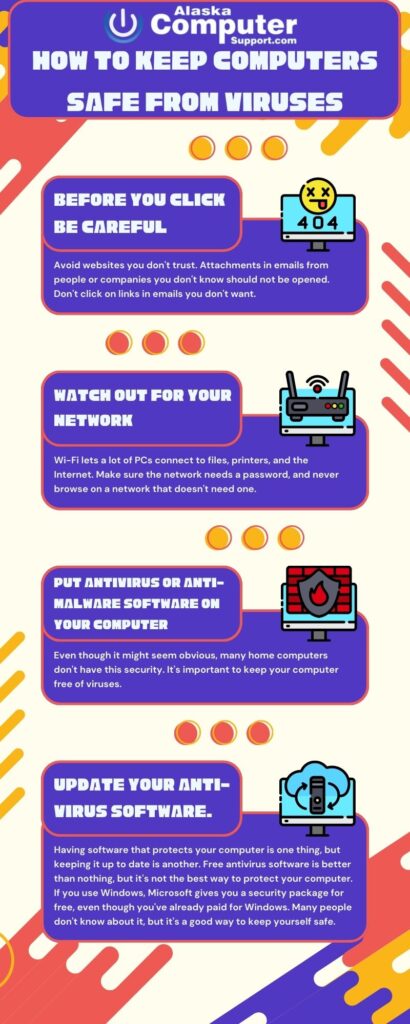
1. Antivirus Software
One of the most effective ways to protect your computer from viruses is by installing reliable antivirus software. Antivirus software is designed to detect, prevent, and remove viruses and other malicious software from your computer. It works by scanning your computer for suspicious activity, and then either quarantining or deleting any threats it finds. It’s important to keep your antivirus software up-to-date, as new viruses and malware are being developed all the time.
2. Regular Software Updates
Another way to protect your computer from viruses is by keeping all your software up-to-date. Software updates often include security patches and bug fixes that can prevent vulnerabilities that hackers can exploit. It’s a good idea to enable automatic updates whenever possible, and to check for updates regularly.
3. Safe Browsing Habits
Many viruses and malware are spread through the internet, so it’s important to practice safe browsing habits. This includes avoiding suspicious websites, not clicking on pop-ups or links from unknown sources, and being wary of downloading files from the internet. Always make sure you are using a secure, up-to-date web browser.
4. Email and File Attachments
Email attachments are another common way for viruses to spread. Be cautious when opening attachments or clicking on links in emails from unknown sources. Don’t download attachments unless you are certain they are safe, and always scan attachments with antivirus software before opening them.
5. Firewall and Network Security
A firewall is a network security system that monitors and controls incoming and outgoing network traffic. It can help block unauthorized access to your computer and prevent viruses and malware from spreading. In addition to using a firewall, it’s important to secure your wireless network and use strong, unique passwords. Consider using a virtual private network (VPN) when accessing the internet from public Wi-Fi networks.
Conclusion
In conclusion, understanding the different types of computer viruses and how they operate is crucial in protecting your computer and personal information. There are many different types of viruses, including boot sector viruses, file infectors, macro viruses, polymorphic viruses, worms, Trojan horses, spyware, and ransomware.